Chips4Makers has officially launched a crowdfunding campaign to produce the Retro-uC, an open-silicon microcontroller capable of acting as a Zilog Z80, MOS Technologies 6502, or Motorola M68K microprocessor.
“I am delighted to announce that the Retro-uC crowdsupply campaign has now been launched. It has taken a little longer to straighten out the last hurdles in production and delivery but now the campaign is waiting for you,” says Staf Verhaegen of the project’s launch, in an announcement on LinkedIn.
“Together with the Crowd Supply staff, the delay has also been used to streamline the pledge targets. Next to the hardware targets now also open silicon development support is included in some of the targets. This is to help to bootstrap the low-volume open silicon movement. This is the first step on the road to low-volume low-cost open silicon. I much appreciate any support or expertise you can provide in this endeavour.”
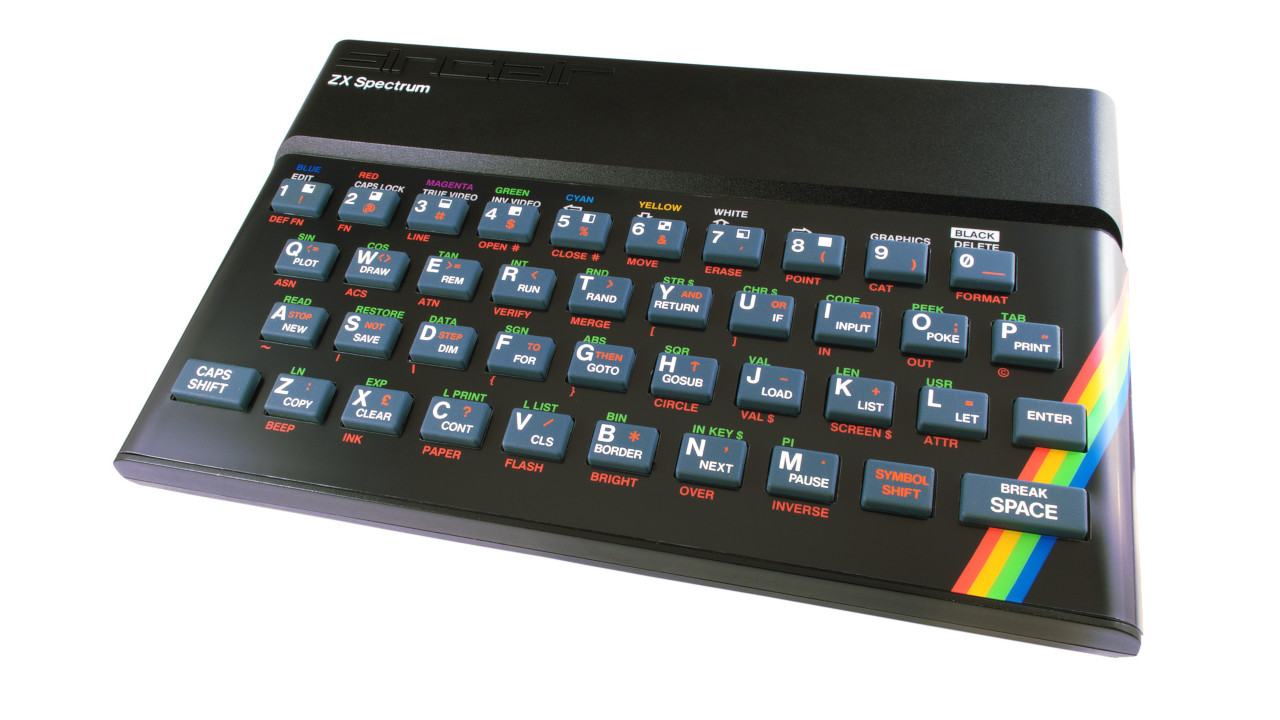
The Retro-uC itself is available as a bare chip, Arduino Mega layout development board, breadboard-compatible breakout, or Perf+2-style prototyping board. In all cases, the chip can run cores designed for compatibility with the classic Zilog Z80, MOS 6502, and Motorola M68K microprocessors, found in vintage computing machines including the ZX Spectrum, Commodore 64, and Commodore Amiga respectively. Both the source code and the tool chain will be released under open-source licences, Staf has confirmed.
More information is available on the Crowd Supply campaign page.
Developer Marcelo Samsoniuk has demonstrated just how flexible the open RISC-V instruction set architecture is by creating his own implementation – in, he claims, just one night.
“Developed in a magic night of 19 Aug, 2018 between 2am and 8am, the darkriscv is a very experimental implementation of the open source RISC-V instruction set,” Marcelo writes of his creation. “Nowadays, after one week of exciting sleepless nights of work (which explains the lots of typos you will found ahead), the darkriscv reached a very good quality result, in a way that the “hello world” compiled by the standard riscv-elf-gcc is working fine!
“At the moment, the darksocv [darkriscv-based system-on-chip (SoC) design] is not so relevant and the only function is provide support for the cache controller as well some basic glue-logic,” Marcelo continues. “The proposal in the future is make possible connect the darkriscv to large external memories, as well make possible connect multiple darkriscv cores in a SMP configuration and maybe provide Ethernet communication. Another possible update for the future is integrate the cache controller in the core, in a way is possible a better flow control.”
The full darkriscv implementation can be found on Marcelo’s GitHub repository, under the BSD 3-clause licence.
Embedded Design’s Ville Baillie is running a series on over-the-air updates for embedded Linux installations, a key feature of being able to keep Internet of Things (IoT) deployments functional and secure, with this week’s instalment looking at the currently-available off-the-shelf solutions.
“Once an Embedded Linux product leaves the lab and enters the real-world, the question of how to update the device will become important to consider,” Ville writes by way of introduction. “Updates are not always necessary, but it’s hard to think of any software that does not have bugs that are discovered at some point. Even if your software is perfect, if the device communicates on networks or the internet with any open-source libraries, security updates may become a necessity.”
In the second part of the series, Ville examines the relative pros and cons of several off-the-shelf solutions for updating embedded Linux platforms: Mender, SWUpdate, and RAUC. “The decision of which system to use really depends on the project,” he concludes. “It seems that Mender is probably easier to get started with, whereas SWUpdate might be useful for integrating with an update system that has already partially been developed in house, and RAUC might be used as an alternative to SWUpdate.”
Part one and part two are available to read now on Embedded.com.
Advertising, search, and computing giant Google has announced the release of a new cross-platform open-source cryptographic library aimed at protecting implementers from common cryptographic mistakes: Tink.
“In cryptography, subtle mistakes can have serious consequences, and understanding how to implement cryptography correctly requires digesting decades’ worth of academic literature. Needless to say, many developers don’t have time for that,” explains Google’s Thai Duong of the project’s inspiration.
“To help our developers ship secure cryptographic code we’ve developed Tink – a multi-language, cross-platform cryptographic library. Tink aims to provide cryptographic APIs that are secure, easy to use correctly, and hard(er) to misuse. Tink is built on top of existing libraries such as BoringSSL and Java Cryptography Architecture, but includes countermeasures to many weaknesses in these libraries, which were discovered by Project Wycheproof, another project from our team. With Tink, many common cryptographic operations such as data encryption, digital signatures, etc. can be done with only a few lines of code.”
While Tink has been publicly available via Google’s GitHub repository for nearly two years, and the company has been using it internally for its own services, it wasn’t until last night’s announcement of Tink 1.2.0 that the library became truly cross-platform.
More information is available on Google’s open source blog while Tink itself can be found on the company’s GitHub repository under the Apache Licence v2.0.
Open-source developer Bootlin has announced the end of its funded programme to develop and upstream open-source mainline drivers for the video processing unit (VPU) hardware in Allwinner’s system-on-chip products, but has pledged to continue best-effort development despite having exhausted the crowdfunded budget.
Bootlin announced its campaign to fund development of an open-source driver bundle for Allwinner VPUs back in February. Following a successful funding run, the company was able to deliver all primary goals by July, making it possible to use the hardware acceleration features of Allwinner’s VPUs using a mainstream Linux kernel for the first time.
Now, with the budget spent and the end of Paul Kocialkowski’s internship at the company, Bootlin has offered a final update on the project. “Over the past six months, we have worked hard to reach the goals announced in the project’s crowdfunding campaign and we were able to deliver most of the main goals last month,” the company writes.
“We have now exhausted the budget that was provided through the crowdfunding campaign: both Maxime Ripard’s time (who worked mainly on the H264 decoding and helping with DRM topics) and Paul’s internship are over, and therefore the remaining work will be done on a best-effort basis, without direct funding,” the company explains. “This will therefore be the last weekly update, but we will be publishing updates once in a while when interesting progress is made.”
Work continues on tweaking the patches for upstream inclusion, adding support for the newer Allwinner H5 and A64 chips, and integrating the userspace drivers with popular open-source media playback software.
The finalised programme for ORConf, the open-source digital design conference organised by the Free and Open Source Silicon (FOSSi) Foundation, has been published ahead of the event’s opening later this month – and with it the news that storage giant Western Digital has become the headline sponsor.
Scheduled for the 21st to the 23rd of September at Poland’s Gdansk University of Technology, the ORConf schedule is packed with talks and workshops covering everything from the RISC-V ecosystem to tools like SpinalHDL, Chisel3, SymbiFlow, and even a talk by project founder Wilson Snyder on Verilator’s 4.0 release.
New to the schedule is a talk by Western Digital’s Zvonimir Z. Bandic on the company’s use of the open RISC-V instruction set architecture (ISA) in storage processing products – a project the company has previously stated will see it shipping a billion RISC-V cores a year, one of the biggest deployments of an open ISA in history.
More details on the event, of which AB Open is a sponsor, can be found on the official website alongside links to register for a free individual ticket or buy a supportive business ticket.
Finally, the Pwn2Own security contest, in which researchers compete to exploit vulnerabilities in popular consumer products in exchange for cash prizes and ownership of the items in question, is to extend to cover Internet of Things (IoT) products for the first time amid growing concerns over the lack of security-focused thinking in their development.
“The Internet of Things is rapidly expanding into all aspects of our lives, from the smart home to the factory floor and connected cars, but products are often rushed to market without enough attention paid to their security,” claims Brian Gorenc, director of vulnerability research for Trend Micro and member of the Zero Day Initiative which organises the Pwn2Own events. “The ZDI is committed to helping remedy this situation by revealing vulnerabilities to vendors and minimising their risk of being exploited. That’s why we’ve extended the scope of this year’s Pwn2Own Tokyo contest beyond the standard mobile devices. We’re looking forward to seeing what some of the world’s best researchers bring to the event.”
Extending what was previously known as Mobile Pwn2Own, the new event will add consumer-oriented Internet of Things products including the Amazon Echo, Amazon Cloud Cam, Google Home, and Nest Cam IQ to the list of target devices, along with popular smartphone products. Each vulnerability discovered and demonstrated is eligible for a cash prize of up to $150,000, while details of the precise nature of the vulnerability are kept private pending responsible disclosure to the companies involved.
Pwn2Own Tokyo is schedule to take place on the 13th and 14th of November during the PacSec security conference in Japan. More information is available on the Zero Day Initiative website.